Newsletter
January 27, 2023
OSINT Monitoring & Analysis by TSARO
Monitoring and tracking potential threats from the dark web, open source, and social media platforms is crucial to maintain the safety and security of the general public and your company. However, many cybersecurity experts, analysts, and researchers that gather and handle this kind of open-source intelligence (OSINT) lack the knowledge, resources, and internal control required to counter an assault successfully.
Making DIY monitoring and analysis prohibitively expensive and developing Intelligence to satisfy each stakeholder necessitates enormous and diverse datasets, various technologies, and hard-to-find expertise. Threat data feeds, and information platforms have been developed in response by vendors in the cybersecurity sector. However, more than each is needed for complete Intelligence and overwhelms teams with clamorous notifications.
Because of this, the usage of managed services has dramatically increased during the past ten years. Today, businesses employ managed services to solve various issues, from endpoints and SIEM management to the firewall and network management.
Overview of OSINT
Open-source Intelligence (OSINT) is the term for any data that can be obtained to identify threats aimed at enterprises from sources, including the dark web, open source, and social media platforms.
Using data from monitoring and analyzing the dark web, open source, and social media platforms, TSARO Labs, OSINT Monitoring and Analysis provides cybersecurity, protective security, and intelligence teams with contextualized, prioritized, and relevant results. As a result, TSARO can make recommendations thanks to their monitoring and analysis, which aid in identifying dangers, thwarting attacks, putting an end to enemies, and mitigating risks.
As a managed service, TSARO offers OSINT Monitoring and Analysis, which provides threat intelligence created especially for the client by skilled intelligence analysts as hardware and software cannot be deployed. Customers engage as a service package. When the trust establishes, TSARO Analysts will begin their inquiry. To supply actionable Intelligence so businesses can make the most use of their internal resources and achieve their goals, TSARO offers this as a managed service.
OSINT (Open-Source Intelligence) tools gather information from publicly available sources. Here are some popular OSINT tools at TSARO we use:
- Google: One of the most widely used search engines, it can be used to find information on websites, images, videos, and more.
- Maltego: A tool that can be used to conduct surveillance and analyze relationships between different pieces of information.
- Shodan: A search engine for Internet-connected devices that can be used to find information on specific types of devices or vulnerabilities.
- Recon-ng: A web reconnaissance framework, it can gather information on domains, IP addresses, and more.
- The Harvester: A tool that can be used to gather information on a specific target, such as email addresses and subdomains.
- OSINT Framework: a comprehensive list of OSINT links and resources that can be used to gather information on a wide variety of topics
- SpiderFoot: an automated OSINT tool that can be used to gather information on IP addresses, domains, and more
- Metagoofil: a tool that can be used to gather information on a specific target, such as email addresses and files.
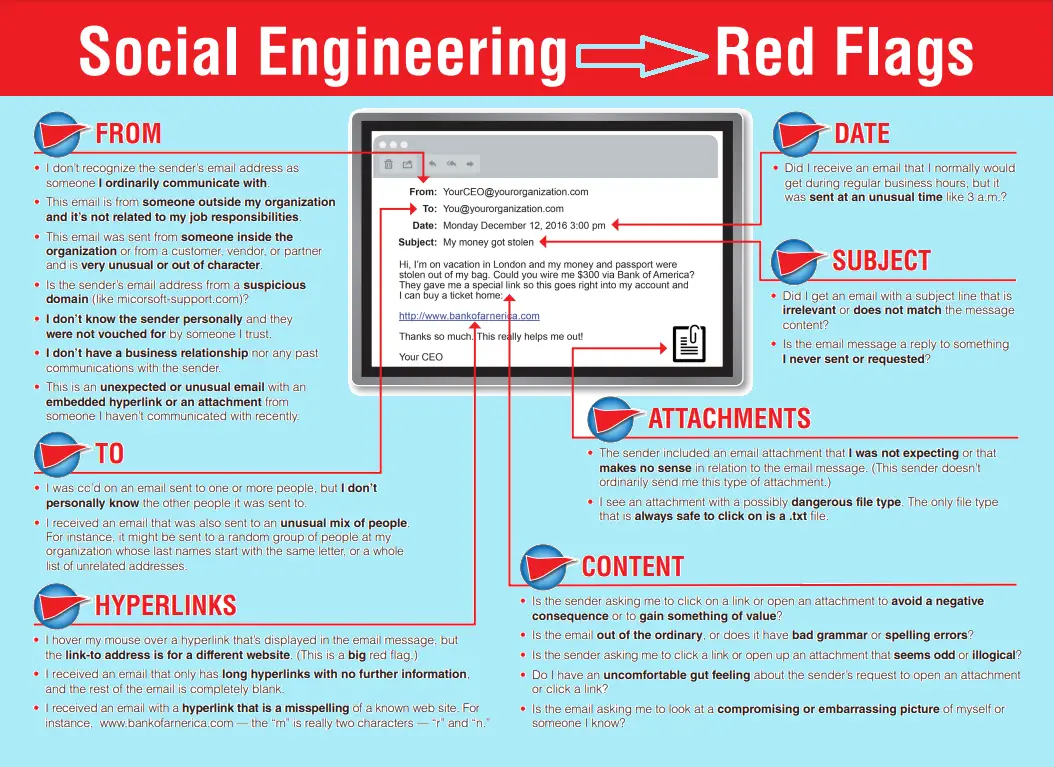
- Social-Engineer Toolkit (SET): A tool that can conduct social engineering attacks and gather information on a specific target.
- OpenVAS: an open-source vulnerability scanner that can identify vulnerabilities in systems and applications.
TSARO is among the first to deliver client-specific threat intelligence as a managed service at scale, thereby providing:
Unmatched Open-Source Collection Capabilities
TSARO gathers and maintains a sizable collection of content to search for references of the client, their brand, key individuals, or frozen assets using a substantial stack of third-party and proprietary tools. To better understand the goals and strategies of threat actors, TSARO experienced analysts infiltrate closed forums and groups using old personas.
Expertise Across All Intelligence Domains
Although various intelligence suppliers offer information on cyber threats, few do so as comprehensively as TSARO. Our analysts are specialists at identifying risks to a client's reputation, fraud and platform abuse proof, physical threats, and third-party danger.
Engagement of Analysts and Client Success
Each customer interacts with a lead analyst and a client success director as part of TSARO's practice of placing cyber professionals at the heart of every engagement. TSARO Client Success Directors are clients' primary point of contact and have an average of over ten years of intelligence experience. Client Success Directors guide clients through contracts, TSARO solutions, troubleshooting, and administrative requirements for their businesses. The TSARO team will examine their results and recommendations before assembling the client's finished intelligence product.
OSINT (Open-Source Intelligence) tools gather information from publicly available sources. Here are some popular OSINT tools at TSARO we use:
- Google: One of the most widely used search engines, it can be used to find information on websites, images, videos, and more.
- Maltego: A tool that can be used to conduct surveillance and analyze relationships between different pieces of information.
- Shodan: A search engine for Internet-connected devices that can be used to find information on specific types of devices or vulnerabilities.
- Recon-ng: A web reconnaissance framework, it can gather information on domains, IP addresses, and more.
- The Harvester: A tool that can be used to gather information on a specific target, such as email addresses and subdomains.
- OSINT Framework: a comprehensive list of OSINT links and resources that can be used to gather information on a wide variety of topics
- SpiderFoot: an automated OSINT tool that can be used to gather information on IP addresses, domains, and more
- Metagoofil: a tool that can be used to gather information on a specific target, such as email addresses and files.
- Social-Engineer Toolkit (SET): A tool that can conduct social engineering attacks and gather information on a specific target.
- OpenVAS: an open-source vulnerability scanner that can identify vulnerabilities in systems and applications.
Customized Intelligence for your needs:
Vendors in the cybersecurity sector have created OSINT-collecting products to enable the scraping and scanning of big data sets from the open and dark web. They are typically offered as a threat feed or platform and are simple to combine with other tools, such as SIEMs but fall short of providing real Intelligence. These techniques merely offer insufficient threat information that needs additional analysis to be usable. Furthermore, because these solutions do not consider the customer’s needs, the insights frequently need the proper organizational context to make the data pertinent to the client.
TSARO, in contrast, only provides final Intelligence that has been gathered and developed by their analysts for the particular problems the client faces. As a managed service guided by analysts, TSARO’s OSINT Monitoring and Analysis provides client-specific threat intelligence.
TSARO’s highly skilled analysts frequently scan the surface, deep, and dark web for signs of breaches, disinformation campaigns, fraud, platform abuse, and physical threats aimed at businesses supported by unique technology and datasets. To guarantee that the Intelligence offered is reliable, fast, and usable, TSARO analysts work as an extension of the client’s team to create, customize, and improve inquiries.
TSARO OSINT Monitoring and Analysis delivers contextualized, prioritized, and pertinent information from monitoring and analyzing the dark web, open source, and social media platforms to cybersecurity, protective security, and intelligence teams. Thanks to their monitoring and analysis, we may make recommendations that assist in spotting dangers, thwarting attacks, putting an end to enemies, and mitigating risks.
OSINT Monitoring and Analysis finds hidden risks on the open, deep, and dark web using analyst-driven threat hunting to offer crucial Intelligence. TSARO analysts create and hone client-specific searches, enabling real-time monitoring of corporate mentions. Additionally, TSARO analysts employ old personas to enter private forums and communicate with threat actors directly. A designated analyst will evaluate threats daily to determine their integrity and urgency, notifying clients of any calls for quick action. If necessary, TSARO can reveal the identities of high-risk threat actors attacking the company utilizing technical links that imply a real-world identity.
OSINT Monitoring and Analysis provides Intelligence for diverse use cases, including:
CYBER: Threats and risks to confidentiality, integrity, and availability of sensitive data, including data leakage and insider threats.
FRAUD: Cybercrime, e-crime, and online fraud. Trafficking in stolen or illegal physical goods, illicit purchases of goods or near money instruments (gift cards, credits), use of stolen credentials, accounts, or payment methods.
PLATFORM: Threats and risks to the trust and safety of an online platform. Misuse or abuse of credentials and accounts, platform abuse including counterfeit apps, malicious content syndication, and API manipulation via bots.
PROTECTIVE: Threats and risks to executives, physical property, corporate assets, and PII takedown capabilities in response to doxing.
THIRD-PARTY: Threats and risks by vendors, suppliers, partners, mergers, acquisitions, and investments. Data leakage of client data by vendors.